On Demand Assessments
Vulnerability Assessment
Gain actionable insight into vulnerabilities in your Infrastructure and Network.
Satius Security’s On-Demand Vulnerability scanning assessment covers Network, Infrastructure, and Applications with actionable results to drive remediation in a prioritized and efficient manor.
Our Vulnerability Assessments will help you achieve the following outcomes:
-
Do you need assurance that you are protected against the majority of critical vulnerabilities hackers are currently exploiting? -
Do you want a prioritized list of vulnerabilities so you can pro-actively strengthen your cyber resilience? -
Do you want confirmation that your patching activities are keeping pace with the threat landscape?
Overview
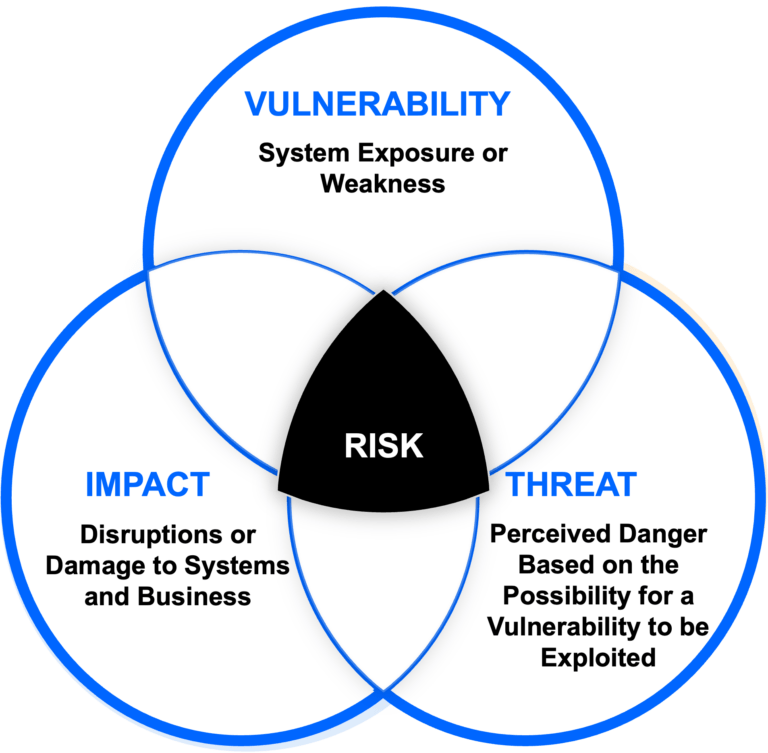
What is Vulnerability Assessment?
A vulnerability assessment is a process that scans your digital assets in search of known vulnerabilities. These are the vulnerabilities most commonly exploited, resulting in data compromise, system down time and reputation damage.
Vulnerability assessments allow you to identify, quantify and prioritize weaknesses within your network, applications, systems, websites, databases and other infrastructure.
BENEFITS
Benefits of Vulnerability Assessments
Achieve validation that your vulnerability management activities are in-line with best practices and you’re keeping up with newly released patches.
By scanning and identifying all assets with a defined range of IP addresses, vulnerability assessments can locate rogue devices on your network that are not listed as authorized assets.
Help achieve and maintain compliance against a range of cyber security standards including PCI-DSS, ISO27001, NIST and others.
When other systems in your environment know that certain machines are vulnerable to certain threats, it allows more efficient incident response in the event of a breach.
Vulnerability assessment scanning will reveal all installed certificates, as well as expiration dates, enabling timely certificate renewals.
More easily identify and review the creation of suspicious new local users, which may indicate a potential security threat.
SCOPE
Scope of Vulnerability Assessments
Network Internal & External
Network vulnerability assessments focus on scanning your network hosts, including connected devices, to identify known vulnerabilities. This can also include virtual environments and their host configurations.
Wireless Network
Wireless network vulnerability assessments test for the presence of unauthorised wireless access points and review the security posture of your wireless network.
Applications
Application vulnerability assessments include testing your web or mobile applications against OWASP’s Top 10 most prevalent vulnerabilities. Testing can be performed as an authorised or unauthorised user.
OUR METHODOLOGY
3-Step Process
Our Vulnerability Assessments follow a 3-Step methodology using a variety of powerful scanning tools to effectively identify a wide range of known vulnerabilities in your environment.
01
Scoping
During this stage, we collaborate with you to grasp the business objectives you aim to accomplish through the vulnerability assessment. We analyze the particular systems slated for assessment, considering how they integrate into your larger environment.
02
Engagement
In this phase, we undertake the vulnerability assessment scanning, making sure all essential information is clearly communicated.
03
Post Engagement
During this phase, we deliver the findings from the vulnerability assessment scanning processes. Our reports offer prioritized lists of identified vulnerabilities within your environment, enabling you to promptly initiate remedial actions to fortify your infrastructure.
Reporting you can trust
We have the vulnerability assessment expertise to select and calibrate the best tools for your unique industry and IT system. We’ll also work with your internal IT department to coordinate a vulnerability scanning schedule that won’t interrupt important systems or services.
-
Detailed findings report -
Highlight of security issues in need of immediate attention -
Remediation guidance
Our security qualifications
Our experts hold numerous industry certifications and vendor specific certified trainings to insure standardized approach and optimal results.

CRTO
Zero-Point Security’s Certified Red Team Operator.

CRTP
Certified Red Team Professional.

OSCP
Offensive Security Certified Professional.

OSCE
Offensive Security Certified Expert.

OSWE
Offensive Security We Expert
OUR SERVICES
Our award-winning security services
Satius’s security services are designed to provide the vital assistance needed to make tangible improvements to your organization’s cyber security posture.
Managed Security Services
Expert help to manage and monitor your choice of security technologies
ASSESSMENT SERVICES
Specialist engagements to uncover and address hidden cyber security risks
Turn Key Solutions
Complete solution delivery on cloud or SaaS with world-class support
Blog
Latest news
We fully understand the challenges SMBs and enterprise face alike to meet security frameworks compliance and ensure overall optimal security posture.
See all blog posts

Use Case
Validating 3rd-Party Managed Endpoint Security with Breach and Attack Simulation

Use Case
Operationalizing the MITRE ATT&CK Framework with Breach and Attack Simulation (BAS): Enhancing Cybersecurity Controls Validation

Use Case
Enhancing Business Transaction Monitoring with Elastic Search: A Success Story
Previous
Next