Cloud Security
google cloud security
Optimize your google cloud security posture
Our Security Controls Validation service is designed to test an organization’s security posture by simulating various stages of a cyberattack, from initial compromise to data exfiltration. The primary goal is to simulate the tactics, techniques, and procedures (TTPs) of real-world cyber attackers to validate the effectiveness of your endpoint prevention and detection mechanisms against emerging threats.
BAS (Breach and Attack Simulation) validates an organization’s security posture by testing its ability to detect a portfolio of simulated attacks performed by SaaS platforms, software agents, and virtual machines. In addition, it generates detailed reports about security gaps and prioritizes remediation efforts based on the risk level. The typical users of these technologies are financial institutions, insurance companies, and more ”
GARTNER
OVERVIEW
Cloud Security Validation for Google Cloud
Migration of workloads to the cloud continues to increase the challenge of defending against the latest cyber threats.
Satius Cloud Security Validation helps security teams keep pace with cloud security posture management by identifying common misconfigurations and overly permissive IAM policies – the two primary causes of cloud data breaches.
Through 2025, at least 99% of cloud security failures will be the customer’s fault, mainly in the form of cloud resource misconfiguration.
GARTNER
KEY FEATURES
Challenges of Google Cloud Security
To ensure that your workloads in Google Cloud Platform are secure, it’s vital to assess your environment regularly. Failure to follow Google’s Shared Responsibility Model and proactively identify cloud misconfigurations can easily lead to cloud breaches.
Google cloud misconfigurations that can lead to incidents include:
-
Misconfigured IAM policies -
Unrestricted access to resources -
Insecure data storage
ADDRESS CLOUD SECURITY ISSUES BEFORE THEY LEAD TO INCIDENTS
Due to the rapid pace of digital transformation, the increasing complexity of cloud environments, and human error, critical security gaps that could enable attackers to compromise your cloud services can arise daily.
Satius Security Validation for Google Cloud helps you to proactively identify and address exposures by:
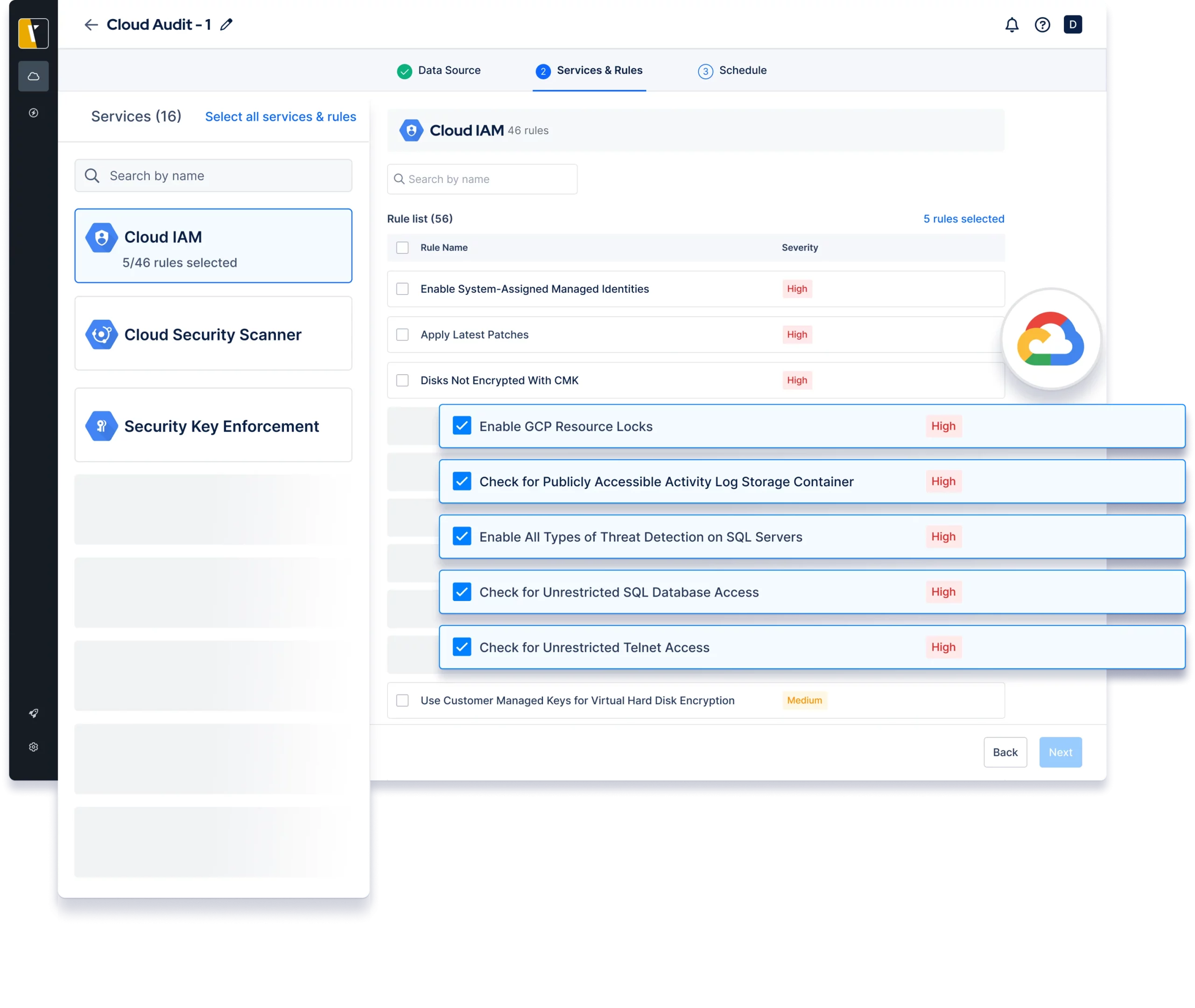
Auditing core Google Cloud services
Satius Cloud Security Validation scans core GCP services to identify critical cloud misconfigurations attackers could exploit. These include excessive privileges, exposed resources, and cryptographic failures.
Simulating privilege escalation scenarios
By simulating privilege escalation scenarios, Picus CSV identifies overly permissive identity and access management (IAM) policies that could enable attackers to compromise GCP cloud services and steal data.
Delivery Models
Our Cloud Security Validation doesn’t just identify issues. It also provides the insights and recommendations you need to understand their severity and respond to risks quickly.
With different and flexible delivery models of our service, we insure clients get the most suitable option for the requirements and the budget.
On-Demand Assessment
Short engagement aimed to validate your cloud security with a executive report and actionable insight findings report.
Managed Service
This continuous service can be offered as a stand alone for cloud security validation or as a part of our broader Continuous Threat Exposure Management CTEM offering.
Turn-Key Solution
Whether you wish to upgrade from on demand or managed service to have the platform delivered from implementation to 1st level support and training.
Our security qualifications
Our experts hold numerous industry certifications and vendor specific certified trainings to insure standardized approach and optimal results.

CRTO
Zero-Point Security’s Certified Red Team Operator.

CRTP
Certified Red Team Professional.

OSCP
Offensive Security Certified Professional.

OSCE
Offensive Security Certified Expert.

OSWE
Offensive Security We Expert
Ready for Cyber Resilience?
Learn more how our Managed Service can help you achieve Cyber Resilience and be an extension of your team without breaking the budget.
