Managed Security Service
CONTINUOUS THREAT EXPOSURE MANAGEMENT as a service
Gain Comprehensive Insights into Your Security Posture with Clear, Actionable Risk Assessments.
Elevate Your Cyber Defense: Transition from Traditional Vulnerability Management to Proactive Risk Management
Book a Demo
or
View Solution’s Brief

How to Manage Cybersecurity Threats, Not Episodes
By 2026, organizations that prioritize their security investments based on a continuous exposure management program will be 3x less likely to suffer a breach.
Gartner
why SATIUS’S continuous threat exposure management as a service?
Amid escalating cyber threats, adopting a proactive strategy is essential.
Our Threat Exposure Management as a Service offers continuous monitoring, threat validation, and tailored security enhancements, utilizing industry-standard frameworks. We present results in clear letter grades, scores, and indices, providing quantifiable measures of threat category management and overall threat mitigation.
-
Reduce Risk Exposure
Leverage real-world attack simulations to identify and mitigate vulnerabilities, minimizing potential threats.
-
Comprehensive Monitoring
Oversee your attack surface across 20 technical categories, ensuring no vulnerability goes unnoticed.
-
Optimize Security Investments
Utilize risk quantification to comprehend the financial implications of potential threats, enabling informed investment decisions.
-
Ensure Compliance
Achieve and maintain compliance with industry standards and regulations, safeguarding your organization’s reputation.
ctem actionable insight
Streamlined, Continuous Protection for Peace of Mind
Satius Security offers CTEM as a managed service. Therefore, providing a framework for ongoing assessments, guidance, and reporting to enhance your overall risk management and cyber resilience.


A holistic approach proceeds from an accurate overview of the risk landscape—a governing principle that first of all requires accurate risk reporting. The goal is to empower organizations to focus their defenses on the most likely and most threatening cyber risk scenarios, achieving a balance between effective resilience and efficient operations.
Executive Management needs Holistic strategy to cyber risk
Companies are rolling out a wide range of activities to counter cyber risk. They are investing in capability building, new roles, external advisers, and control systems. What they lack, however, is an effective, integrated approach to cyber risk management and reporting.
McKinsey & Company

A holistic approach proceeds from an accurate overview of the risk landscape—a governing principle that first of all requires accurate risk reporting. The goal is to empower organizations to focus their defenses on the most likely and most threatening cyber risk scenarios, achieving a balance between effective resilience and efficient operations. Tight controls are applied only to the most crucial assets. The holistic approach lays out a path to root-cause mitigation in four phases.
Cyber risk is now as important a priority for the leaders of public and private institutions as financial and legal risks. Facing a rising threat level and the magnitude of the potential impact, executives are insisting on full transparency around cyber risk and effective ways to manage it actively.
CISOs: Elevate Your Cybersecurity Reporting to the Boardroom
Struggling to bridge the gap between technical cybersecurity metrics and what your board actually wants to see? You’re not alone.
Download our free guide:
“CISO’s Guide To Reporting Cyber Security”
That’s why we’ve created the “CISO’s Guide to Reporting Cyber Security“—a step-by-step resource to help you:
- Present cybersecurity insights in a language the board understands.
- Align security metrics with business goals and priorities.
- Build trust and demonstrate ROI on your cybersecurity investments.
Request a quote >
Free Consultation
What is Continuous Threat Exposure Management Framework (CTEM)?
Book a Demo
or
Download Datasheet
Experience Proactive Cyber Risk Management Today:
Satius Security brings the CTEM framework to life with ongoing assessments, expert guidance, and actionable reporting—empowering your organization to strengthen risk management and build cyber resilience.
Streamlined, Continuous Protection for Peace of Mind.
Satius Security operationalizes CTEM framework to provide an ongoing assessments, guidance, and reporting to enhance your overall risk management and cyber resilience.
Scoping
Identifying an initial scope of the attack surface with a plan to extend it as the program advances.
Discovery
Discover assets and their risk profile, identifying security gaps including misconfiguration of security controls and vulnerabilities.
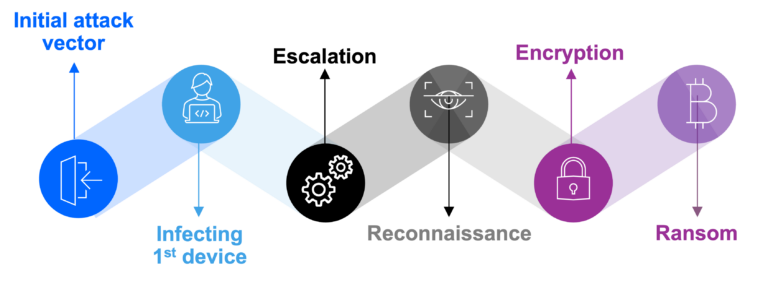
Validation
Assessing the likelihood of attack success, analyzing all potential attack paths, and verifying the effectiveness of the detection, response, and remediation processes.
Prioritization
Prioritizing identified gaps and remediation efforts covering the asset’s business criticality, likelihood of the asset’s being exploited, and availability of compensating security controls.
Mobilization
Ensuring the teams almost frictionlessly operationalize the CTEM findings.
Continuous Threat Exposure Management
No organization can protect against every cybersecurity event. Instead, commit to tackling exposures that most threaten your business
Scoping
Discovery
Validation
Prioritization
Mobilization
Core Threat Exposure Management Components
Empower Your Security with Industry-Leading Validation and Monitoring
Our solution is offered in two ways to accommodate your needs and budget. Basic Proactive Threat Management Aligned with Established Security Frameworks such as FAIR and MITRE ATT&CK. Advanced to enhance Your Defense Strategy with Advanced Risk Management
Unified Threat Insight
Security Controls Validation
Attack Surface Monitoring
Social Engineering
Vulnerability Scanning
Unified Threat Insight CTEM as a Service quantifies your threat exposure with defensible metrics—expressed as Scores, Grades, and Financial Impact—making risk understandable and actionable at every level. Our assessments span over 20 technical modules to provide a holistic view of your Attack Surface, measure the effectiveness of endpoint, network security, Phishing Campaigns, and Infrastructure Vulnerabilities.
Tailored for both executive and technical users, our dashboards transform complex data into actionable insights, empowering teams to drive Cyber Resilience and make informed decisions quickly.
Visit Link
Security Controls Validation Leveraging MITRE ATT&CK’s structured methodologies, our solution simulates real-world threats to validate endpoint and network defenses, security controls across common attacker tactics, techniques, and procedures (TTPs).
Add Detection & Response and Cloud Security Posture assessments for a more comprehensive view of your security controls’ effectiveness, with actionable recommendations for improvement.
Visit Link
Attack Surface Monitoring Identify vulnerabilities across 20 technical categories, ensuring visibility into key areas like credential management, patch status, DNS health, and third-party risks. Our non-intrusive assessments provide insights into attack surface exposure.
Visit Link
Social Engineering Assess employee security awareness against phishing attacks, one of the most common entry points for attackers. CTEMaaS uses data from our Attack Surface monitoring—such as leaked credentials and social media activity—to design risk-based phishing campaigns tailored to employees’ roles within the company.
Visit Link
Vulnerability Scanning Conduct thorough internal and external vulnerability scans to detect and prioritize vulnerabilities in network and infrastructure, enabling proactive mitigation before exploitation.
Visit Link
Expand your threat exposure management
Tailored Add-Ons for Comprehensive Security Management
Customize Your Threat Management Solution to Fit Your Unique Needs with modular add-ons that address specific organizational requirements, enabling clients to build a complete security posture.
Book a Demo
or
Download Datasheet
Cloud Security Posture Management
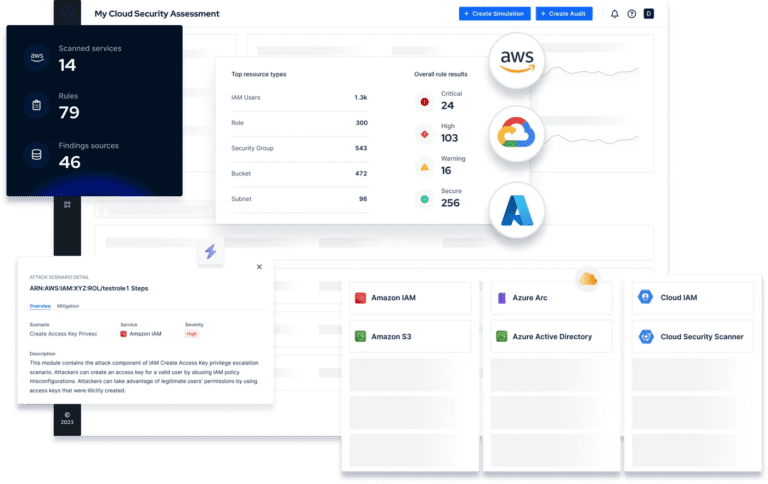
Secure AWS and Azure
Satius Cloud Security Validation helps security teams keep pace with cloud security posture management by identifying common misconfigurations and overly permissive IAM policies – the two primary causes of cloud data breaches.
Learn More
Threat Detection Rules Validation

EDR & SIEM alert and log validation
Boost Detection Effectiveness. Increase your detection capabilities. Get rid of false positives. Mitigate risks swiftly.
Learn More
Dynamic Application Security Testing
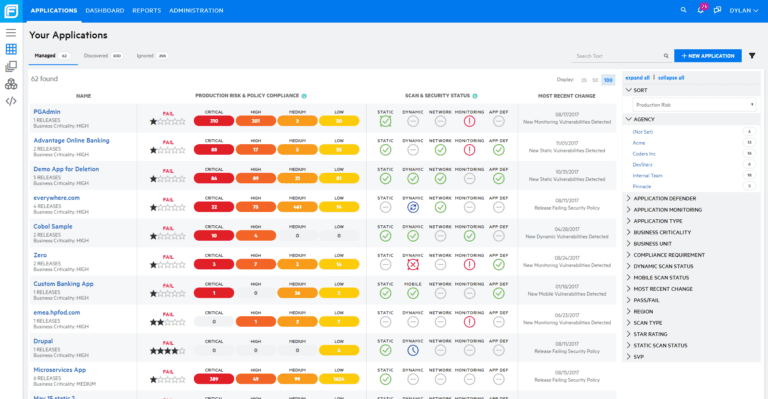
Comprehensive AppSec using Fortify
Enhance application resilience with Webinspect dynamic application security testing to identify and validate high risk security vulnerabilities in running applications.
Learn More
Static Application Security Testing
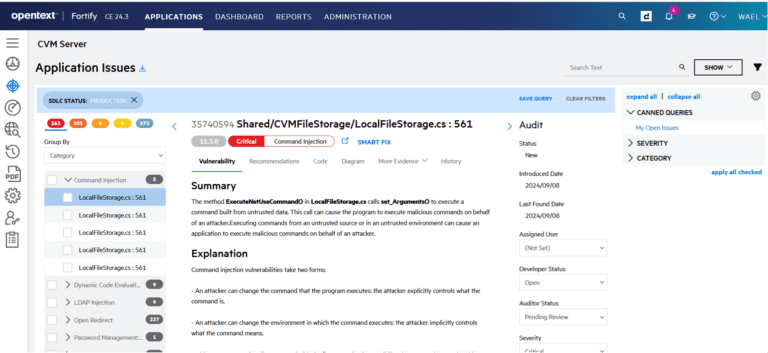
Comprehensive AppSec using Fortify
Leverage Static Code Analyzer for static application security testing (SAST) to build security into the development process. Static Code Analyzer pinpoints the root cause of the vulnerability, prioritizes results, and provides best practices so developers can code more securely.
Learn More
3rd Party Risk Intelligence

Manage Vendors’ Risk and Compliance
Evaluate and manage risks posed by third-party vendors, utilizing contextual data to prioritize remediations.
Learn More
Web App Penetration Testing
Expert Led – Advanced Tools
Identify and remediate web application vulnerabilities before they can be exploited.
benefits of threat exposure management
Benefits of Satius Security’s Threat Exposure Management as a Service
Satius Security offers TEM as a managed service. Therefore, providing a framework for ongoing assessments, guidance, and reporting to enhance your overall risk management and cyber resilience.
Reduced Breach Risk
Identify and mitigate vulnerabilities before they are exploited
Enhanced Compliance
Stay aligned with regulations like PCI DSS, HIPAA, and GDPR
Increased Efficiency
Free up your team to focus on high-priority tasks with automated monitoring
Reporting
Get the answers Executives need to provide directions with actionable insight reporting and defensible data to drive improvement and resiliency.
Exper-Led
The program is managed by certified expert cybersecurity engineers with the knowledge and expertise in all phases of the TEM program.
Adaptable Add-Ons
Tailor your security strategy to address your organization’s specific needs
DISCOVER HOW SATIUS CAN DRIVE YOUR CYBER RESILIENCE
Threat Exposure Management as a Service helps the Executive Management get the answers they need with defensible data to drive your Cyber Resilience
Book Free Consultation
TESTIMONIALS
What our clients say about us

Tedd Long
CSO
Partnering with Satius Security has been a game-changer for our organization. Their expert team and proactive approach have provided us with unmatched peace of mind in today’s cyber landscape.

Steve Jablonski
VP of IT
Working with Satius Security has been instrumental in bolstering our company’s cybersecurity defenses. Their proactive solutions and round-the-clock support have significantly enhanced our resilience against cyber threats. I highly endorse their services to any IT team looking to elevate their security posture.

Elie Hamouche
CTO
Satius is a professional IT Security Company that always gives the best value. We benefited from their recommendations and expertise to mitigate findings.

Basheer Altayeb
Head of IT Risk-Cybersecurity
We have been working with Satius for years to understand and minimize risks. The team performed multiple projects from vulnerability management to security controls validation. very satisfied with the value received.
We work with organisations across a range of industries
-
Finance -
Government -
Retail
-
Healthcare -
Education -
Industrial
Other industries
Clients
Global Clients
Satius Security has been the cyber resilience partner to Enterprise and Government clients in the United States, Middle East, and Europe such as: